JWT – Everything you need to know!
Welcome to Secumantra! In this post, we are going to understand what exactly is JWT and why JWTs are so popular in web applications these days. So let’s get started –
Introduction and Purpose
JWT stands for JSON Web Token and mainly used in OAuth workflows. These tokens are kind of protected data structures and carries information primarily about token issuer, client claims, expiration time etc.
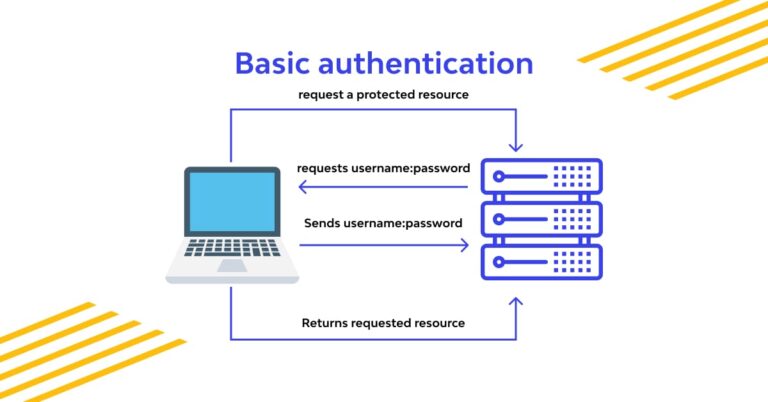
The most common scenario for JWTs is authentication. Typically client (application) requests a token, issuer (server) issues a token and resource (API) consumes a token. Resource (API) has already established a trust relationship with an issuer. For example – when we try to use some third party app using our Google ID, we are provided a consent form for confirmation and we say ‘Yes’ as we trust Google. It is a type of OAuth 2.0 workflow.
If some terminologies are new to you, don’t worry now. We will discuss these in a separate post.
So JWT has all the information needs to be shared and it is cryptographically signed as well. It is the additional feature which makes it tamper proof. Signing also makes it authentic so that recipient trusts the issuer. It is exactly the same way we used to sign a document and as our signature is unique, the other party trusts the authenticity.
Here is a real life example of a JWT, it is a long string which look like –
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiJnb29nbGUuY29tIiwiZXhwIjoxNzAzMzAwNTIwMjAsImF1ZCI6Imh0dHA6Ly9zb21lUmVzb3VyY2UiLCJzdWIiOiJTZWN1bWFudHJhIiwiY2xpZW50IjoiYWJjIn0.8YLTpZNvrZsyKq9BHxzcqXKKm1gJWZaWo3uVIFlx2kMStructure of JWT and How JWT Works
JWT is divided into three parts, mainly two parts as third part is the signature. The core of any JWT is claims. Claims are the JSON data inside the JWT. It’s the data you care about and want to pass along securely to someone else.
- Header
- Metadata
- Algorithms and keys used
- Claims
- Issuer
- Audience
- Expiration
- Subject
- Other custom claims
- Signature
Let’s try to understand this by an example with JSON format. As JSON is native format for Javascript which is a plus point for JWT and one of the reason of its wide acceptance.
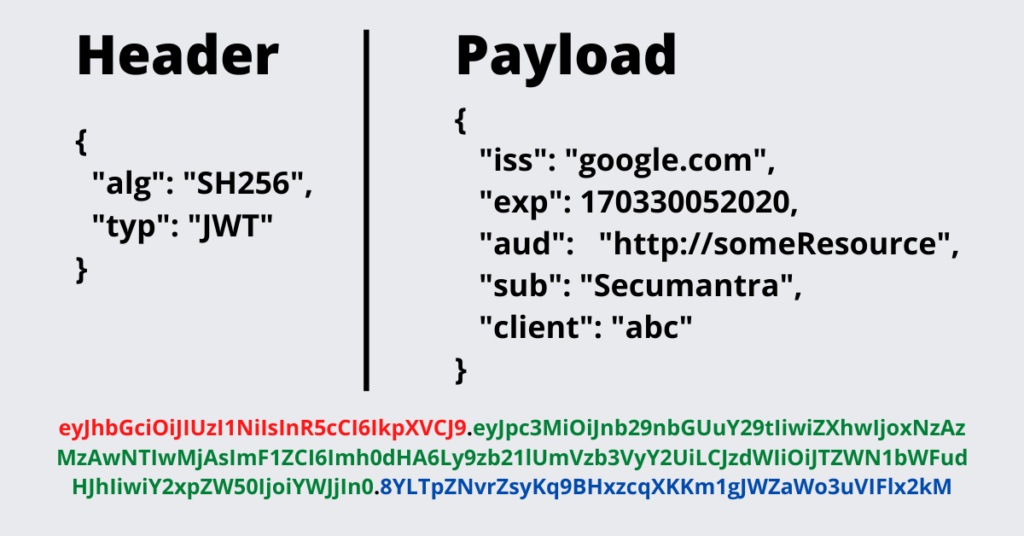
The header contains the metadata for the token and typically mentions the type and the encryption algorithm. In this example, JWT header declares that the encoded object is a JSON Web Token and it is signed using the HMAC SHA-256 algorithm.
If we do base64 encoding of header part, we have the first part of JWT (string with red color).
In the context of JWT, the claim contains the information we want to transmit, and that the server can use to properly handle JSON Web Token authentication. There are multiple claims we can provide; these include registered claim names, public claim names and private claim names.
Registered claims are not intended to be mandatory but rather to provide a starting point for a set of useful, interoperable claims. Examples are –
- iss: The issuer of the token
- sub: The subject of the token
- aud: The audience of the token
- exp: JWT expiration time defined in Unix time
If we look at our JWT claims and we do base64 encoding, we have the second part of our JWT (string with green color).
Now the last part – signature! It is generated by combining the encoded header and the encoded payload, and signing it using a strong encryption algorithm, such as HMAC SHA-256. The signature’s secret key is kept with the server so it can verify existing tokens and sign new ones.
encodedSignature = HMACSHA256( base64UrlEncode(header) + “.” + base64UrlEncode(payload), PRIVATE_KEY)
This gives us the final part of our JWT (marked as blue string). Now we have the JWT which can be sent over the wire and can be used by web applications for subsequent calls.
One of the intent is to keep these JWT size is really small so that we can use them mobile workflows as well. It is also equally important in today’s microservices world. Producing and consuming JWT is beyond the scope of this article, but all major platforms have proven libraries to implement JWT in your application.
Summary
JWT is a type of security token (Json Web Token) mainly used in authorization workflows as mentioned by OAuth2.0. JWTs are key aspects to all of the protocols in web application security space today. In this post, we mainly tried to understand the structure and working of JWT.
Although JWT signature provides authentication and keeps JWTs safe from tampering, we need to understand that core data (claims) is just base64 encoded (not encrypted) and can be easily decoded using any free tool. So it is advised to avoid sensitive information being part of payload.
Thank you for reading and will see you in our next discussion. Stay Safe, Stay Secure!