Broken Authentication & Session Management
Welcome to Secumantra! In this post, we will understand the number two vulnerability in the OWASP Top Ten 2017 version which talks about broken authentication and session management. We already know what is OWASP and OWASP Top Ten, please read more about it here.
In short, OWASP (Open Web Application Security Project) is a nonprofit foundation that works to improve the security of software. OWASP Foundation is globally recognized by developers as the first step towards more secure coding. It releases OWASP Top Ten List every 2-3 years sharing the most critical security risks to web applications.
Introduction
Generally, broken authentication refers to weaknesses in two areas: session management and credential management. Attackers can use either hijacked session IDs or stolen login credentials to exploit vulnerabilities in a web application.
It is another very nasty vulnerability because an attacker is able to log on to a system and impersonate the victim. Also it is a fairly broad risk as there are many ways an attacker can break the authentication and session management.
In recent years, broken authentication attacks have accounted for many of the worst data breaches. Despite being widely documented for years, it still holds the second position in OWASP’s 2017 list of the top 10 most critical web application security risks.
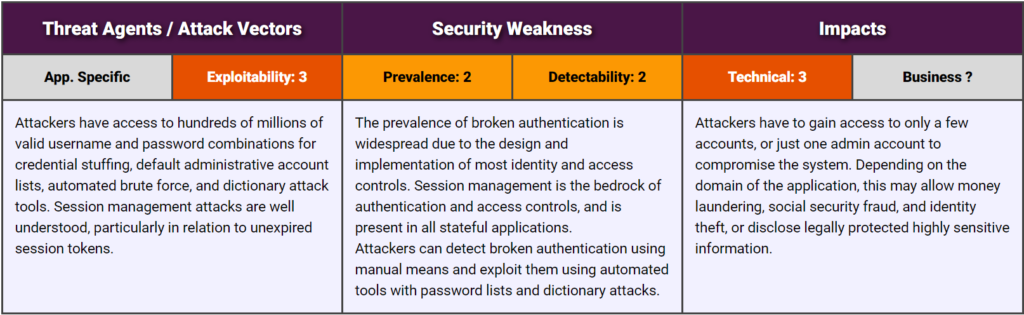
OWASP Risk Rating
Let us look at the OWASP risk rating matrix –
Looking at the attack vector, exploitability is average. In terms of to weakness, it is a very widespread risk because systems are often poorly designed when it comes to managing authentication and sessions. The detectability is average. An attacker normally need to go through and attempt to exploit a weakness in order to actually identify its presence.
Technical impact is severe because attacker actually being logged in as the victim. Now the business impact is solely dependent on the nature of the web application and we need to ask ourselves what would it mean if an attacker was able to login to the website.
What is Session Management?
Modern web applications require users to login to access their online accounts. Generally this is done using a username and password. With this information, a web application will assign and send each logged in user a unique session ID that serves as a key to the user’s identity on the server. A web session is now established which can be treated as a sequence of network transactions associated to the same user within a period of time.
These session IDs commonly take the form of cookies and URL parameters. Session management deals with how you define the parameters of that session. For example, how long can a session last before you automatically log a user out? How do you issue and revoke session IDs? How securely are they linked to a user’s IP address?
It’s important to note that a user establishes an authenticated session with the web application once the user logs in. Consequently, OWASP states that the session ID of an authenticated session is temporarily equivalent to the strongest authentication method used by the application, such as username and password. A hijacked session ID is as strong as a stolen login credential.
Session Management Attacks
- Session Hijacking: Without appropriate safeguards, web applications are vulnerable to session hijacking, in which attackers use stolen session IDs to impersonate users’ identities. The most straightforward example of session hijacking is a user who forgets to log out of an application and then walks away from their device. A hacker can then continue their session.
- Session ID URL Rewriting: Another common avenue for session hijacking is “URL rewriting.” In this scenario, an individual’s session ID appears in the URL of a website. Anyone who can see it (such as via an unsecured Wi-Fi connection) can piggyback into the session.
- Session Fixation: One commonly overlooked best practice is to rotate session IDs after a user logs in, instead of giving a user the same ID before and after authentication. Web applications that fail to do this are vulnerable to a session fixation attack, which is a variation of session hijacking.
What is Broken Authentication?
When a user signs in to a website, the site uses a proprietary algorithm to generate a unique session ID. The visitor’s device then uses that session ID as a key to their identity for the remainder of their login session. All of this information has to be sent back and forth between the visitor and the server. If that information is not encrypted and is sent as plain text instead, it’s possible for someone to intercept a visitor’s session ID and/or credentials to impersonate that same visitor. This is especially true when operating on a public network (like a coffee shop wifi) that anyone else can access and possibly intercept.
Another approach an attacker could take is attempting a brute-force attack wherein they repeatedly try common passwords in an effort to guess a user’s correct password. It is also possible for attackers to forge session IDs if they are not randomly generated. For example, if an attacker intercepts several legitimate session IDs that are enumerated, it is possible to guess the next legitimate session ID and access the site fraudulently. These are commonly referred to as man-in-the-middle attacks.
Some examples of broken authentication are listed below:
- Credential Stuffing: When attackers access a database filled with unencrypted emails and passwords, they frequently sell or give away the list for other attackers to use. These attackers then use botnets for brute-force attacks that test credentials stolen from one site on different accounts. This tactic often works because people frequently use the same password across applications.
- Password Spraying: Password spraying is a little like credential stuffing, but instead of working off a database of stolen passwords, it uses a set of weak or common passwords to break into a user’s account. For example ‘123456’, sports names, curse words, and the ever-popular “password”. Password spraying is a type of brute-force attack, but it often slips by automatic lockouts that block IP addresses after too many failed login attempts. It does this by trying the same password, one user at a time, rather than trying password after password on a single user.
- Weak Password Reset: There are many examples of exploitation through password reset process because they are solely dependent on being able to answer personal information about the person. For example, the name of the school or what their first car was. This information is often discoverable for well known public figures.
- Phishing Attacks: Attackers typically phish by sending users an email pretending to be from a trusted source and then tricking users into sharing their credentials or other related information. It can be a broad-based attempt that hits everyone at an organization with the same phony email, or it can take the form of a “spear phishing” attack tailored to a specific target.
Common Defenses
Broken authentication attacks are devastating and common, but they are also highly preventable. By putting a few safeguards in place, you can make your organization a much less appealing target for attackers.
Better Session Management
- Transport Layer Security: In order to protect the session ID exchange from active eavesdropping and passive disclosure in the network traffic, it is essential to use an encrypted HTTPS (TLS) connection for the entire web session, not only for the authentication process where the user credentials are exchanged. Additionally, the
Securecookie attribute must be used to ensure the session ID is only exchanged through an encrypted channel. - Session Timeout: Web application automatically ends sessions at some point, either after logout, a period of no activity, or a certain length of time. Session length needs to be defined to suit the type of user and the application they’re using. A streaming-video service might want their sessions to be weeks long, but a banking app should automatically log users out after a few minutes since the risk of a hijacked session is much higher.
- Rotate and Invalidate Session IDs: The best way to prevent session fixation is to issue a user with a new session ID after login. Similarly, sessions and authentication tokens must be immediately invalidated after a session ends, so attackers can’t reuse them.
- Don’t Put Session IDs in URLs: There are so many ways that URL rewriting can end up exposing session IDs, so your safest bet is not to go that route. Use cookies generated by a secure session manager.
Tighten Password Policies
- Implement Multi-Factor Authentication (MFA): OWASP’s number one tip for fixing broken authentication is to “implement multi-factor authentication to prevent automated, credential stuffing, brute force, and stolen credential reuse attacks.” MFA provides an extra level of security by demanding an additional credential that’s harder for attackers to fake, such as a biometric scan or one-time code.
- Enforce Strong Passwords: Regarding brute force attacks, mentioned earlier in this article, it’s a good practice to have password requirements for all registered users on a site (this includes admin accounts, especially!). Strong passwords do not include complete words, but rather are a mix of random letters (both uppercase and lowercase), numbers, and symbols, so the password can’t be easily guessed.
- Don’t Store Passwords in Clear Text: A strong password storage strategy is critical to mitigate data breaches that put the reputation of any organization in danger. Ensure that credentials are stored in encrypted format using strong and proven encryption technique.
- Use Breached Password Protection: Use an identity and access management (IAM) platform with breached password protection. When the platform discovers a compromised credentials cache, it will notify you if any of your users were compromised. Those users will be locked out until they change their passwords, so attackers can’t use their compromised passwords against you in a credential stuffing attack.
Guard Against Attacks
- Conduct Workplace Phishing Training: Teaching your workforce how to spot malicious emails is a project you must take seriously and update frequently. As phishing attacks get more sophisticated, they become harder to spot, and the only way to combat this threat is to keep your staff informed.
- Implement Brute-Force Protection: Limit the number of invalid login attempts, after which disable the account for a specific period. This limitation will discourage the attacker.
- Employee Anomaly Detection: A sophisticated IAM system doesn’t look at just logins and session IDs to determine whether a user is legitimate or malicious. It should also flag other types of suspicious behavior. Anomaly detection will alert you if, for instance, an employee logs off at 10 p.m. in North America and logs back on at 3 a.m. in Bangladesh.
Summary
Authentication and session management in a web application is often implemented incorrectly. It could then result in an attacker impersonating a valid user. It allows these attackers to compromise passwords, keys, or session tokens, or to exploit other implementation flaws to assume other users’ identities temporarily or permanently.
Web applications will become more attractive to attackers as companies move more sensitive data to the cloud. Broken authentication has made it relatively easy for motivated attackers to slip by because even companies with big security budgets often overlook these basic security flaws. It’s a little like barring every window in your home while leaving the front door wide open.
There are several options for dealing with authentication-related attacks, from basic security controls such as password policy and account/IP lockout, to advanced solutions such as MFA and session management controls. Attackers prefer short paths and rarely attempt long paths. As a best practice, several strategies should be utilized. That’s why defense in depth is very important when dealing with application security.
Thank you for reading. Stay Safe, Stay Secure!