Top 10 Tips for Smartphone Data Security
Welcome to Secumantra! In this post we will discuss about a topic which is important for not only application developers but also to normal users of mobile devices.
Mobile devices and smartphones have become so common in today’s world. In addition these devices are connected to internet and information is being exchanged continuously. This not only brings new possibilities, but new challenges as well.
As devices are being used in various new ways and the amount of data increases, it is really important that your smartphone is secure for many reasons. You may keep personal data on it and if your phone was lost or stolen, this would be lost. Moreover your personal information may be hacked from internet pages you have visited or from the smartphone itself.
To help you navigate your device in a secure way, we’ve created a list of top ten mobile security tips to keep your device data safe. Lets us discuss them one by one.
1. Use Screen Lock
Generally all smartphones offer different types of locking mechanisms. A ‘pattern lock’ (pattern that is drawn on the screen to grant access) is most widely used screen lock. If your phone is stolen or lost any finger traces can sometimes be seen and accessed on the screen. So, ensure that the screen is cleaned regularly.
Also you can set a pass-code, which is a better alternate. You can set a PIN easily memorable for you but difficult to crack for someone else. If your phone supports, fingerprint scanning and facial identification is also an excellent option. It is faster and easier than memorizing an unlock code.
It is a good idea to password-protect mobile apps that contain personal data, such as banking, email or shopping account. So even if you give your phone to someone, these apps cannot be accessed easily.
2. Use Two-Factor Authentication
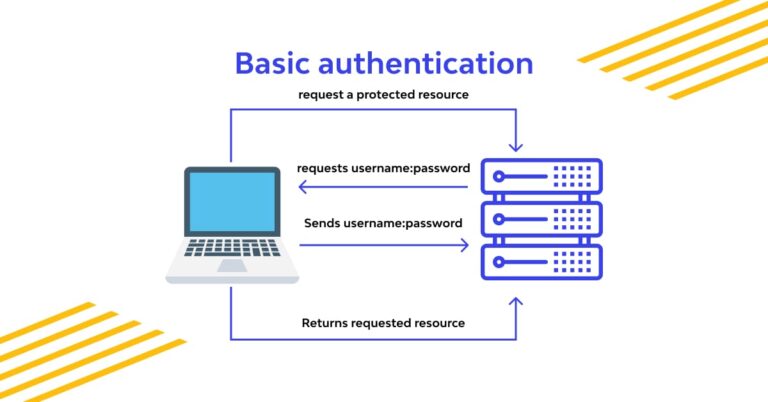
Two-factor authentication (2FA) uses something a user possess in addition to what he knows, e.g. OTP (One Time Password) sent to your mobile phone in addition to the login password.
Although it needs an extra step, it offers another solid barrier to accessing your private information. Wherever possible 2FA shall be used for information critical apps like banking, online shopping or business emails.
Two-factor authentication is much easier to use now with mobile OTPs and bio-metric scanners.
3. Update Mobile OS and Apps Promptly
Mobile phone operating system updates improve your software experience and also contain security enhancements. Most people frequently ignore or postpone system and app updates notifications. The longer you wait to update your phone or laptop, the more out of date your systems are, making you an easier target for hackers.
It is important to stay up to date with OS updates, specially when these updates contain security enhancements. You can see if your phone’s OS is up to date, generally from ‘settings’ in “about phone” or “general” and checking for “system updates” or “software update.”
4. Avoid Using Public WiFi
We can access the internet on mobile devices anywhere and everywhere we go. Most people don’t think twice about jumping on a free public Wi-Fi connection, but people operating devices with sensitive personal or business information on them should exercise caution.
While free wifi can save us on data, it’s important to be aware of unsecured networks. In general, businesses like reputable hotels and event venues have a vested interest in maintaining the security of their Wi-Fi users. However, free public Wi-Fi in areas like shopping centers, cafes, airports, parks or gyms, is often far less secure.
5. Manage App Permissions and Access Control
Check the apps on your phone to determine whether they have more privileges than they need to get the job done. You can grant apps permissions like access to the camera, the microphone, your contacts and your location. Keep track of which permissions you’ve given to which apps, and revoke permissions that are not needed.
Android users can find app permissions in the Application Manager under Device > Application in some Android versions. For iPhones, go to Settings and tap on Privacy, where you’ll see a list of all permissions and the apps you’ve granted them to.
Generally permissions are also requested when a new app is installed or being used for the first time. So always be cautious when clicking ‘allow’ when asked for these permissions.
6. Backup Your Data
Even if you prepare yourself for the worst, disasters can happen. If your data is compromised, you may not be able to access it anymore – or in the worst case scenario, it could be deleted permanently. This becomes critical when you also use your phone for official or business purposes.
That’s why you need to back up the data on your mobile devices regularly. This shouldn’t be a one time activity but should back up your data regularly to avoid major losses of data. This is a general good practice, it protects your important documents and images in case of any loss.
For an Android phone, make sure “Back up my data” and “Automatic restore” are enabled in the settings and then sync your data with Google. For an iPhone, choose your device in the settings and then back up to iCloud.
7. Know Source of Apps
Don’t just download any app to your phone. While iPhones only run apps from Apple’s App Store, which vets all apps sold from the platform, standards are not quite as high on Android.
The Google Play Store has made progress in ensuring its apps aren’t running malware, but the Android platform allows installation from various, less-regulated environments. The best way to avoid malware on Android is to stick with the Google Play Store, unless you are sure you can trust an independent app from somewhere else.
8. Safe Internet Browsing
Be careful when accessing a web browser on your smartphone as it can be easy to accept messages that pop up. For example agreeing to save user details and passwords might make it easy to remember for later, but unfortunately others can do the same if they gain access to your phone.
If any security warning pop up when looking at a website, take note of it and leave the website if needed. Also, ensure any banking or shopping sites where you put in secure information have a padlock in the address bar to ensure that the site is encrypted.
Make sure you always look at the URL and make sure the ‘http’ has an ‘s’ at the end. This ensures that the URL you are about to click on is secure. For more details, read here about HTTPS and man-in-the-middle attack.
9. Watch Bluetooth Usage
Bluetooth is not generally seen as a security risk as it has a relatively short range. However, hackers have been known to remotely access a phone through bluetooth if they are in range.
Do not keep your Bluetooth connection enabled when you are not using it. Viruses and malware are easily spread through Bluetooth connection. Set the bluetooth configuration to ‘non discoverable’, so that people searching for nearby devices can’t see yours.
Any unknown requests that pop up through a bluetooth connection, such as an offer to ‘pair with a device’ should be ignored or declined. A hacker in range could make use of your device through bluetooth if it is not secured.
10. Remote Wipe
If the worst happens and your phone is lost or stolen, you may want to protect your data by wiping data quickly and remotely.
You can also use remote tracking if you loose your phone. On Android it is called ‘Find my Device’ and on Apple iPhone it is called ‘Find my iPhone’. From here, you can remotely disable your phone if needed.
Bonus Tips!
- Do not keep your sensitive information like passwords or banking credentials stored in plain text format on your mobile.
- Do not share your OTP with anyone. Your OTPs are meant to be a secret, so you must never share your OTP with anyone over calls, SMS or in person. No banks or reputed companies will call asking for the OTP.
- Do not open suspicious e-mails or the attachments that come with them.
- Do not use your phone’s removable memory card in other devices if you cannot guarantee they are secure. The devices may have malware on the memory card, which runs on your phone without your knowledge.
- Do not connect your phone to other devices with a USB cable or Bluetooth if you cannot guarantee that they are secure.
Summary
The technology we use can make us a target for viruses and cyber attacks if not secured properly. There is a huge increase in number of mobile device users in recent years. Due to wide reach of internet, more and more data is generated and exchanged every day. We need to protect that data from harmful agents and hackers.
This becomes even more important when mobile device is being used for business purpose. Your smartphone is now a critical extension of your business. Its tiny footprint often makes it easy to lose or misplace, or a target of theft. Take advantage of the security features you already have at your fingertips, instill good security habits in your staff, and, if necessary, purchase additional security software.
There is no single solution to secure your smartphone and personal information from hackers. The key is to practice as many best practices as you can, as often as you can. So let us start with the top ten tips we discussed here.
Thank you for reading! Stay Safe, Stay Secure!